Why don’t we quantify the brain? What I want to argue today is that we need a shift from diagnosis and treatment, to wellness and prevention. And that we have the data to do it.
Archive (Page 1 of 2)

We’re at a time of huge expansion of the Internet outside of the kinds of Internet connections and devices that we’re familiar with. We’ve seen some of that over the past few years as we’ve moved from laptops, desktop computers, to smartphones and tablets and we’ve seen a big increase. Right now instead of a tablet and a laptop at home, you’ve got a tablet, two iPhones, and a desktop computer.
What we’re trying to do is to see over the horizons, looking at essentially a five-year time frame, and identify what will be the cybersecurity landscape in that context.
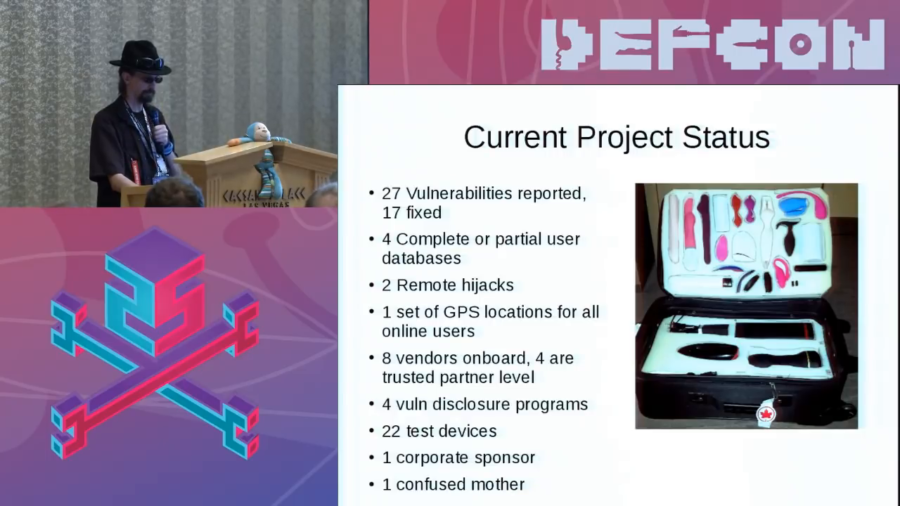
A large number of IoT research firms…yeah, they don’t want to look at this. Because there are stigmas around sex. We have a very weird thing in North America about sex. We’ll watch all the violence we want on television but you can’t see two people have sex.

I am profoundly envious of people who get to write about settled domains or sort of settled states of affairs in human events. For me, I was dealing with a set of technologies which are either recently emerged or still in the process of emerging. And so it was a continual Red Queen’s race to keep up with these things as they announce themselves to us and try and wrap my head around them, understand what it was that they were proposing, understand what their effects were when deployed in the world.

This is a moment to ask as we make the planet digital, as we totally envelop ourselves in the computing environment that we’ve been building for the last hundred years, what kind of digital planet do we want? Because we are at a point where there is no turning back, and getting to ethical decisions, values decisions, decisions about democracy, is not something we have talked about enough nor in a way that has had impact.
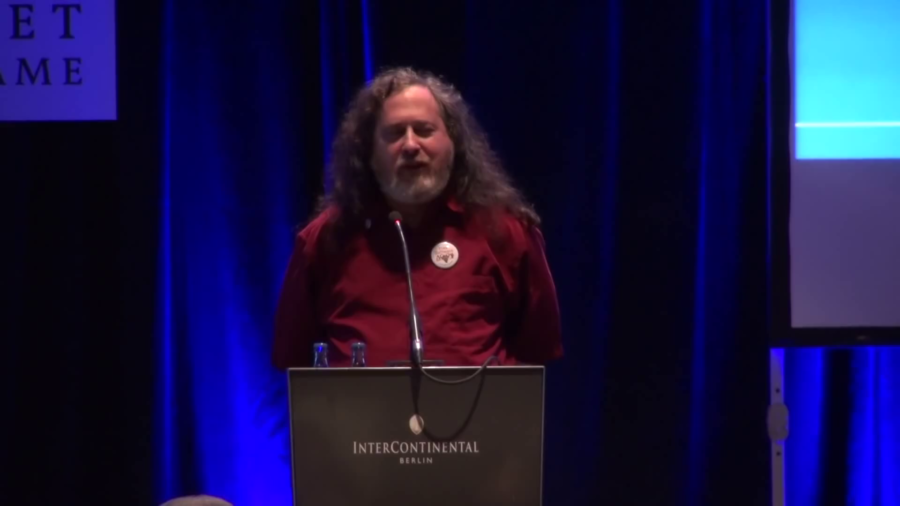
So, thirty years ago if you wanted to get a new computer and use it you had to surrender your freedom by installing a user-subjugating proprietary operating system. So I decided to fix that by developing another operating system and make it free, and it’s called GNU, but most the time you’ll hear people erroneously calling it Linux.

Sure, cyberspace is about people and data. But it is also about applications. And devices. And the indirect and non-obvious relationships between all of this. It creates a very complicated and exciting ecosystem. One that is capable of dramatic innovation, and dramatic exploitation.